DOCS + FAQ
Frequently Asked Questions
and documentation rolled into one :-)
Understand all this in just half an hour.
It is that simple!
In this document the word "merchant" is someone who has a website where you are welcomed using your own Homing Space username.
If you have already created your Homing Space, then you can test your usernames with
this "Test Merchant" here Note that you will have to use the same phone and the same browser where you created your Homing Space
Why this? My browser already saves my passwords! (or Microsoft/Facebook/Google has Single Sign on)
True. There are many many password managers. Even browsers save passwords quite well. There are several single-sign on systems too -- from various large companies. The problem is NOT just about convenience.
Homing Space is about trust -- both from your end as well as at the merchant's end.
Homing Space achieves trust because it is fanatical about privacy, your own control over your own data. And complete security. It does NOT want you to be a puppet for someone's hidden agendas. Not even our agenda (hmmm... we don't have anything hidden, BTW) !
It is about your identity protection, your personal and private data... it is about longevity and graceful use.
Password managers, browser saving your password, single-sign ons etc are often
very temporary solutions; if indeed they are real solutions. They just apply a local balm. They do NOT address the bigger issues of privacy, data-theft, impersonation. You often become a puppet at the hands of
others.
Homing Space is the ONLY system where you knock on the door of a merchant. Then the merchant comes to your location and welcomes you to enter their site -- All that happens under your full
control.
How can this even work? I never heard of Merchants coming to "my location" Where is this location?
"My location" is the domain my.homing.space on the browser of your own phone!
This confusion is quite understandable. For quite a long time now, we have been conditioned to think that the only way to enter a website
is to give a username and password there -- that is, at the merchant's site.
However pause for a moment and think of this: For thousands of years; when we knock on a friends door -- they dont ask for our
username and password. Instead, they come to the door where you are standing and they ask "Who are you?" You then reply "It is me. <INSERT NAME>"
Your friend hears you from other side of the door,
notes the voice that he heard, and lets you in!
Homing Space is almost as simple as that. Let me extend that analogy.
With Homing Space, you knock on the
door of a merchant, leave an open press-type padlock there and return back. The merchant comes to you and passes a box to you saying: "You just knocked. Possibly you want to come to my premises. Here is a box locked with your padlock . Inside the box is a special ticket only for you, to get into my premises. I will leave it here and go"
As
you have the key to your own padlock, you open the box; get the ticket left by the merchant in the box and now you can go to that merchant's premises with that ticket.
In our case, if you want the jargon: we use
a sophisticated two-factor system based on the latest cryptographic techniques working inside your browser on your own phone (and not at our server)
Therefore
your phone is "your location" Your Homing Space is present INSIDE your own phone; specifically inside the browser of your phone; at this precise address: my.homing.space
The merchant
encrypts a ticket, and comes and gives it to the browser on your phone The browser at your end knows for sure that it was indeed the merchant who came specifically to welcome you. Now, you have the private key to decrypt
the code. Therefore you now let yourself in with that decrypted ticket.
You can see the video we have which gives another metaphor -- that of a debit card and ATM machines to withdraw money from your bank.
What is "asymmetric" encryption? Why should I care?
Encryption means converting a message to something that others cannot understand at all -- For the other person to understand, he would need to decrypt it.
There are two ways this encryption and decryption
can be done: The symmetric method and the asymmetric method.
The symmetric method is to encrypt the message with one system (you can call it a "trick phrase" or "password" or "key" instead of 'system')
Then to decrypt it the other person uses the SAME sytem/trick/password/key.
The issue with symmetric system is that if a man-in-the-middle can get hold of the transmission of the encrypted message, he
can also be assumed to get the trick phrase too! So even if the message reaches the other person, there can be someone else who has read and misused your original message.
Therefore Symmetric encryption
is never used for transmission. It is NOT used at Homing Space. We use asymmetric encryption. In this system, each person gets TWO keys -- a public key and private key. These two keys are mathematically
related.
Specifically, if one has a copy of the public key -- it is impossible for that person to figure out the private key. Another characterestic of these two keys is that
if one were to encrypt a message using the public key of a person; the ONLY way to decrypt the message would be by using the private key. So if the private key is kept secret by the user; then ONLY that user
can decrypt such encrypted messages.
This is explained in the following figure; where Bob sends some data (some message) to Alice in an encrypted fashion.
Bob gets a copy of the Public Key of
Alice -- and he can now encrypt a message and send it to Alice. ONLY Alice can decrypt it; as she has the Private Key part of the pair of keys. There is absolutely no chance of any man-in-the-middle attack.
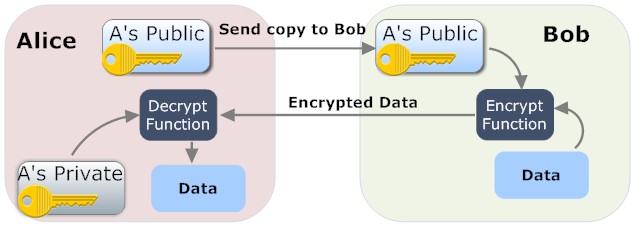
In case of Homing Space, it is our service that gives Bob the public key of Alice. So Bob is the merchant in this documentation. What is NOT shown in the above image is that Bob ALSO has his own pair (i.e. Public
and Private Keys)
Bob also sign the message which he sends to Alice, using his own signing Public key -- that way, when Alice opens the box (i.e. decrypts the message) to get the special
site key that Bob sent in the message, Alice needs to be sure that it was indeed Bob who sent it and nobody else.
So what is signing?
Note: In the figure below which explains
"signing" -- it is Alice who is signing and sending a message to Bob I wish I had got a figure where Bob sends the signed message to Alice -- because in Homing Space, I am assuming Bob is the merchant and Alice is the user. But neverthless, let us proceed assuming it was Alice who signed and sent a message to Bob...
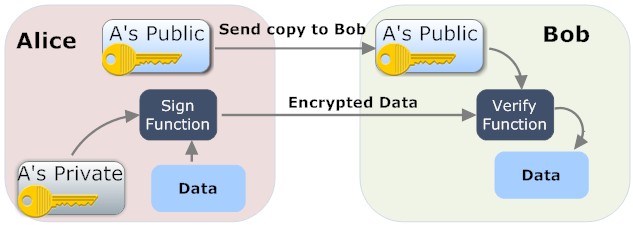
Alice signs the message using her own private key. The term "signing" means that a crptographically secure code is generated on the fly; which acts as a fingerprint of the message being signed. This can ONLY
be done by Alice using her private key.
When Bob receives the message, he ALSO receives the signature code sent by Alice. He now has within his own browser, a clever algorithm
that verifies the origin of that signature. To do that, the browser uses Alice's signing - public key.
How much does this cost?
To the end user, it is all free. For merchants that use this system, it is totally free up to the trial period mentioned on the pricing page. The trial starts from the time when the merchant gets the secret-sauce to use
on their site.
We never ask for money or identity from merchants to begin using this system. Merchants ONLY have to create their own Homing Space first. The persona used there would be managing
user's entries.
After the initial trial period, we charge the merchant a very tiny amount per user entry into the merchant site via Homing Space.
I believe Two-Factor Authentication systems are the best. How does Homing Space compare?
Homing Space indeed is a highly secure Two-Factor System. People need to understand exactly what is meant by "two-factors" and why that is needed.
When you have a username and password as the method
to enter a site; the site just has ONE factor that is checked. That is why sites rarely allows people to register a username and password and ALSO immediately allow the user to use the entire site.
Instead,
merchants usually ask for a second factor at the time of registration -- which is your email address for them to confirm whether it was indeed you who wanted to register. That is the reason we cannot get registered to sites
by unknown people; just because they happened to know our email address.
That "confirmation loop" can be regarded as a "weak" second factor -- or a second route to "hold" you down to your identlty.
Why
weak? because such a confirmation is never done again. Next time you login, you do so with just the username and password. So that means registration was some kind of two-factor, but logins are all single-factor.
There are stronger two-factor systems too. An ATM* debit card that you use to withdraw cash from the ATM machine, uses a very strong two-factor system. There the two factors pins you down with two implicit
questions
a) What do you have? Answer: The card itself
b) What do you know? Answer: The PIN code (known as ZIP code in some countries) of the card.
Thus the bank who dispenses the money is sure
that it is indeed you. The bank used two different routes to verify if it was indeed you. Such a TWO factor identification is used ALL the time, whenever you use your ATM* debit card.
Homing Space is a very secure 2FA system! The two-factors are answered as follows:
a)
What do you have? Answer: Your own phone
b) What do you know? Answer: The password that you had memorized; the one that encrypted your Homing Space data on your phone
In fact, quite soon on our
roadmap; Homing Space will be introducing even more factors to make this a multi-factor authentication system and not just a 2FA system.
Why should this be trusted?
The entire system works on some trusted, audited, cryptographic libraries that works within the browser of your device. Not ours. You can get any technical person to read the HTML and Javascript code that we use. We have clearly documented the entire system right inside the web page itself! See the next question
How do we know that personal data is really private?
You can easily see the code that we use in the browser. Our HTML is well documented. Just use this link in chrome and ask some technically savvy person to go
through the HTML. You will find that NO PRIVATE DATA of the user is even sent to our server.
ALL PERSONAL data is saved in the browser you used on YOUR own device. The ONLY data that does get saved in our servers
are the public - keys of the asymmetric cryptographic system implemented by Homing Space
Are there similar systems such as Homing Space?
Mozilla had introduced "BrowserID" few years back. Its intention was very similar to Homing Space.
However, it had important differences -- for example; it still used email addresses. Homing Space actually
does not use any form of conventionally known IDs such as email address or phone number for it to work. It also required you to check the email you gave to their system once a day. Unfortunately, they did not communicate
well regarding their technology. People did not understand how it worked -- and so it fell out of use.
That experience is why we are making Homing Space so transparent. Someone with reasonable amount
of knowledge in HTML and Javascript and crytography, can see our code and understand how our system works internally.
Apple recently came with their own "Login using Apple ID" Isn't that much simpler than Homing Space?
Apple's strategy is just a variation on a commonly used strategy -- which is to use "disposable email addresses" which hide your actual email address.
It is a good strategy and achieves something simple. Your actual
email address is not given over to the merchant. The disposable address comes in between and protects your privacy.
However, it is not clear how much of your data would get collected by Apple as
it stands inbetween the user and the 3rd party app/website -- there is not much clarity on this important point.
There is nothing greatly different being done by Apple to protect you-- you can still get spam
and other privacy violations though with a bit of a guard -- as you can dispose off, of the intermediate email given by Apple.
Where is the app for it?
The earlier version of Homing Space did not have an app. But now we have an Android app that you can get from http://onelink.to/homingspace Soon, an IOS app will also be available
for iPhones. The app is quite tiny and will not collect anything meaningful from your phone. We need only the DeviceID and nothing much else. Your phone should have an active SIM card -- to ensure that we are handling a
genuine user.
To get your Homing Space, just install that app; start it; and then click on the Start button. Once your Homing Space gets created; some restoration code is displayed in the phone browser. Store that
restoration backup code in a safe place. You would need it in case you lost/changed the phone and you want to restore your Homing Space on a new device
If Homing Space is to be used on the phone, then how do I use a merchant's website on my computer?
You would enter such merchant's website first on the phone using your Homing Space there. Then the merchant will give you a special OTP that you can use on your regular computer browser.
I had created my Homing Space But I now tried using it and the browser says that I don't have it! What to do?
Homing Space is created ONLY on your phone browser. On Android it is the Chrome browser and on Apple devices it is the Safari browser. If you have more than one browsers; make sure that you used the same one which was used to create the Homing Space. For your privacy's and security sake; your Homing Space in one browser CANNOT go to any other browser.
If I upgrade my phone or the browser in the phone, will the Homing Space inside my phone get affected?
The current techniques for upgrading either the phone operating system or the browser apps (Chrome and Safari) should NOT change your Homing Space. However buying a brand new phone and discarding your old phone
can pose a small difficulty.
You can use the "Restore" button on our app to restore an earlier backup of your Homing Space.
Why should we not use OAuth and OpenID connect systems?
The OAuth system is full of privacy concerns. It is also overly complicated and confusing. The lead author of the OAuth specification resigned leaving behind a note. Read that note here.
We
feel Oauth is also a rather sneaky way for big companies to collect, aggregate and do data-analytics on your data. For example; Facebook and others entice people to use their systems claiming that they add value. But what
really happens is that the users are merely puppets in their hands.
The user does get some value for participating in such sites (e.g. village gossip. But maybe I am harsh. They do add some value)
However
the main intention is to get users to click on advertisements or even see the advertisements for which they charge huge to the other merchants advertising there. The users own life, frankly, is all secondary.
The
OAuth system gives you the feeling that you can easily get into other websites. What is frankly happening there is that the other websites are actually hand-in-glove with Facebook (and other such sites)-- these two then
do further data analytics on you; and then you get to see the same advertisements on both the sites - -violating your privacy.
OpenID in its initial days did superficially work similar to Homing Space;
(E.g. It too avoided passwords as much as possible)
However it was fraught with security and user perception problems. Nowadays, OpenID has morphed into something that rides on top of OAuth systems. and really
does not add any much value. It has completely veered away from OpenID of the olden days; execepting for the name.
OpenID Connect is quite convoluted and confusing too.
Also, each of the
top-sites (you know which ones!) decided to create their own variations of the OAuth standard -- so it is actually not really a standard anymore.
To put it simply: There are lots of privacy concerns with current
authentication and authorisation systems. But I think I already mentioned this before.
But it was said that OAuth is supposed to unify everything?
Ideally yes. But that did not happen. If these large companies had implemented a strictly common standard of OAuth then we would not have had buttons that state "Sign-in with Google" or "Sign-in with Facebook" Instead
we would have seen just one button "Sign-in with any account of yours that implements OAuth" That way the customer would have had the freedom to choose where he/she kept his/her personal data -- and then
his/her data would spring forth from there to all other locations.
But that never happened. It looks like that will not happen in the future too.
As we mentioned earlier; you, the user is merely
the puppet on which these sites grow. Your life, actually, has no real meaning for them -- as long as you click on the advertisements displayed, it is all fine for them.
The number of people who are disappointed by the OAuth and OpenID connect system is not just the original author, but many other companies have also stopped supporting it.
What is authentication? and authorisation?
Authentication answers the questions: "When you come in here, Are you the same person who came yesterday here? And will you be the same person who will come again tomorrow? " -- It does not really concern
with the actual identity of the person from a legal point of view.
Authentication is what is needed to ensure that you are that one unique person all the time.
Authentication theoretically can
be done without knowing anything about that person. We do it all the time in the real world. When we see a stranger on the road; we know for sure it was a human there. We are very sure that the same person cannot
be somewhere else too at the same time. That is an authentic experience. Yet, we do not know anything about that stranger -- not even the stranger's name!
Unfortunately, such deep authentic experiences are
not possible on the Internet. At the very least you need a consistent username to point to the authentic person -- which is what Homing Space does. You have to supply your Homing Space username (and
nothing else).
Authorisation is not the same as Authentication.
Authorisation answers the question: How do I get personal information on that unique person? Again here too the question
is not really about the identity from a legal stand point. The information about you here refers to things like birthday, your blood-group, your spouse's name and so on.
There is no way to really verify whether
the values given by the authenticated person, are true -- just that the system who gets authorized information simply takes in all that at face value because it believes that such data is about the same unique
indiviual everytime -- because the authentication system proved that it is the same individual in all interactions.
Unfortunately, the OAuth system muddled up both these concepts together and people get confused.
The sign-in using Google and Sign-in using Facebook etc confused people even more -- because each implemented their own "variation" on the OAuth system.
Can the Homing Space authentication can be shared with others?
Since your phone is a crucial part of our system; it would be difficult to share your Homing Space with others. Because even the password that was memorized will ALSO have to be shared for the other person
to impersonate you.
Think of your phone as your ATM* debit card. Of course one could share that ATM* card. But then you need to share the PIN (sometimes called ZIP) code of that debit card too to the
same person you gave the card to.
Otherwise it would be impossible to withdraw money. Such sharing does ocassionally happen between close relations-- and when that happens, the person sharing the card
knows the risk involved.
Casual sharing of just your phone will NOT break your Homing Space system. Why? Casual sharing does not mean you share your password of your Homing Space too!
Don't tell me you don't harvest my email address or phone numbers?
We do NOT HARVEST any information about you. We do not even ask for them when you create your Homing Space . We really cant even contact you!
The App also serves as a notification system -- so businesses
that allow Homing Space can notify you of important messages. You can easily turn off those notification on your phone/tablet.
What about our Aadhar card number/Social Security Card number/Bank account no ... ?
No. We do not even ask for them when you create your Homing Space.
But I saw some merchant that uses the Homing Space system, ask for an email address! Some even asked for phone number too!
The entry point form is supposed to ask just ONE question: Enter using your Homing Space; or some similar message. Nothing else. If a merchant is asking at that point additional information, please
register a complaint with us; citing us the address of the website.
However, at the end of the process; and you are about to authenticate yourself at your own Homing Space on your phone; some
merchants may then ask you to provide additional data about you. Such as an email address of yours, phone number, etc. Read the specific details on their website on what data they expect to receive. If they
are asking for something more; or something that you do not want to provide; do not enter that particular merchant's site!
But doesn't Homing Space harvest the user's data during authentication?
No we do not. You can easily see the HTML and Javascript code that we use in the browser. It is quite clear that the form that gets displayed for collecting data goes DIRECTLY to the endpoint specified by the merchant. We do
NOT come in the way at all or harvest any data.
Why do some merchants ask for additional data?
That is a good question. There are many situations where a merchant can add value to a user without knowing exactly who that user is, without wanting additional user's data such as email, phone number etc.
For
example; merchants can earn money by actually giving real service to you -- without making you a puppet to click on advertisements. We can think of a whole slew of applications/websites/service providers who can give
quality value to users; and at the same time FULLY protect the user's privacy.
But let me not thrust my moral stance on to others. There could be merchants who do good work and they ALSO need additional data.
The
additional data on you maybe a phone number, or a Telegram account (to give chat service) and so on. Read the documentation of such merchant's website and check for yourself exactly why they want additional data on you.
If
you think the merchant is not entitled to take data from you, and yet they do; please send an email to us at admin@homingspace.com (Use a disposable email address if you doubt that we may send out marketing emails,
etc to you) We will soon setup a forum where you can also register a complaint.
Why do merchants ask for data immediately during authentication? Why not later?
We implemented the request for additional data, via a form that gets presented to you just as you are authenticating yourself -- because we wanted to ensure that you know exactly what is being given out to a merchant, just
as you enter the site. Again, let me repeat, we simply send that form DIRECTLY to the endpoint registered by that merchant. We do NOT harvest anything.
One major advantage of this method; is that the
you are ABSOLUTELY sure of the origin of the data used by merchants. Such data is ALWAYS emerging from your own Homing Space only, and nowhere else. You need not authorize anyone else to do it for
you.
But then where is the user's data?
The user's data is all inside the phone browser of the user. In that specific browser where his/her Homing Space personas were created. It is NOT with us at all.
So what user data is held by the company behind Homing Space?
We hold the user's public keys. Nothing else from the user.
In truly secure cryptographic systems -- such as the one used by Homing Space; the user gets two keys. One is called a private key. And
the other is called a public key. They work in tandem, as a pair.
When a user creates his/her personas inside Homing Space, two such pairs are used. We store ONLY the public keys
of these two pairs; per user. Why two pairs? Why not just one, you may ask. Well, one pair is used to lock a "metaphorical box" containing data. The other is for signing that data.
Will you harvest or sell the Homing Spaces when the user base grows?
We cannot even access each of our user's own data -- let alone collect and sell them! Homing Space is a highly distributed system.
That means, each person keeps his/her OWN data. Each person enters
a Homing Space enabled website using his/her own private key. All that is stored ONLY on that user's own phone -- nowhere else.
It is completely impossible for us (or anyone else either!) to aggregate
all that distributed data together. In short, the data simply cannot be even reached -- let alone sold.
But you do have the public-keys of the users. Will that be harmful?
In cryptography, the term public key actually means that it CAN indeed be seen by the public. So there is NO harm that is done whatsoever just because we stored them.
The asymmetric encryption system ensures that
the public key can ONLY be used with its corresponding private key. As the private key is kept privately and that too encrypted by the users -- there is NO value with us having only the public key. We cannot use it
to pry or do any harm.
Without the corresponding private key, the public key is just a jumble of alphabets and numbers. We can ONLY use the public key for encrypting some data and sending it to the person
who has the corresponding private key -- which is what Merchants do through this service. Nothing more. Sending the encrypted message to someone else makes no sense, as nobody other than the one with the private key
can decrypt it!
We are open to ideas on ways by which these keys can be accessed freely by anyone from the public and we can also make our own hard-earned revenues. As the system has just been launched, we are keeping
these public keys with us and anyone can use them from us at an extremely low charge.
BTW, each corresponding private key is on each individual user's own phone. As explained earlier; it is impossible to aggregate
all of that together into one big list. Not by me. Not by you. Not by anyone.
Great! I created my Homing Space. But I cant use it anywhere... Where are the merchants?
If you have created your Homing Space, you can test your Homing Space usernames with the test merchant here. You can even participate in our Wiki,
where you can get an account using the Homing Space you setup
Note that you will have to use the same phone and the same browser where you created your Homing Space.
We are doing our level
best to spread the word regarding Homing Space. We hope you will also spread the word!
As a user, the websites I use; simply do NOT use Homing Space. Then what?
We are soon implementing a simple password manager application for end users. That application will help the user store their current usernames and passwords.
You can always use that to keep track of your current
passwords -- as a quick reminder for helping you login to other sites that simply refuse to change to Homing Space. We hope you will write to such sites and insist that they too adopt Homing Space
Is it really so secure? Does it protect users from phishing attacks?
Yes, it is fanatically secure! Even social engineering techniques such as phishing would be rare. Why are we making such a bold statement? After all, phishing is kind of a clever psychological trick -- a hacker
sets up something that looks like a merchant page -- just to deceive the users.
Well, without Homing Space, phishing did work with several users for one simple reason: Users were entering those
merchants sites directly at that merchant's location -- and not at your phone!
In case of Homing Space; the actual entry point -- strangely enough -- is at your phone and not at the merchant's
site. You are asked for the password a YOUR location (i.e your phone) so how can now phishing work? All you have to remember is to check the browser when you are entering your password.
The address where you provide your single memorized password should always be https://my.homing.space/finalize.yaws
Let
us say for some reason, the hacker presented you with the page that you fill on your own device -- what would it achieve? It will surely NOT pick up data you have at the merchant! It could pick up some of your personal
data (birthday, etc) That is much less harmful than losing the work you had on the Merchant's site.
BTW, picking up data from you also is quite impossible because the hacker has no capability to pretend
to be the merchant (there are some secret codes that a merchant uses with us)! That is practically an impossibility.
As a merchant, how do we start using the Homing Space way of authentication and authorisation?
Implementing Homing Space based authentication and authorisation system is extremely easy. We have a form that any merchant can use -- it will create the required "secret" between us and that Homing Space.
Each secret is different for each website of the merchant.
As a merchant, we already have our own authentication system. How do we start using the Homing Space way of authentication and authorisation?
Implementing Homing Space based authentication and authorisation system is extremely easy, You need to carry out the steps explained in the preious answer.
If you already have another way of getting
in your users; you can either implement our system as an additional method to get inside your site -- or you can completely switch over.
To make it even more easier; you can use our sister service;
simplysign.in which can act as a trusted intermediary.
What is simplysign.in? Do we HAVE to use that too?
No simplysign.in is ONLY for merchants and that too it is optional for them.
Simplysign.in just an optional site for merchants who want to implement Homing Space with
practically no coding. It acts as a trusted intermediary. When a merchant uses simplysign.in to let people into their site, nothing changes for the end user.
This is how simplysign.in works. Think of it as a two-sided system.
From one side it would implement the connection to Homing Space and on the other side; it will connect to your website using a username and the hashed-password,
silently.
You need to just make a couple of API calls to simplysign.in so that simplysign.in knows the hashed password of your users.
You also need to instruct your users to get their
own account at Homing Space. Note that the name of one of the persona should be the one they used as a username at your website.
If you take this route, your website can be Homing Space enabled in 10 minutes or so, with very little coding at your end.
I am a merchant. I can see how Homing Space works. Now instead of using Homing Space, can I implement a variation of the same?
Homing Space is not a complex system for those who understand cryptography. With folded hands we request you to join hands with us, instead of working on something similar. The world has suffered too long
because of people coming with subtle variations on one standard -- See the mess that OAuth and OpenID created.

If you
have any suggestions, please do write to us at admin@homingspace.com. and we can incorporate your suggestions and acknowledge you too. For major suggestions, we will surely partner with you too.
We are considering
the possiblity of making this a federated system too. If you have suggestions along those lines, we welcome those too.
What are the real benefits to a merchant's website?
There are many benefits. Firstly, no hacker would have the incentive to get user data from a merchant site. Why so? Earlier; hackers enter weakly implemented websites and retreive usernames and passwords. Or these hackers buy
the list of usernames and passwords from corrupt officials of websites.
Then such thieves use the same username and password and try and enter other more important websites. They do this because they
know very well that lots of users use the same username and password everywhere. Now this kind of theft is simply not possible because it is impossible to do anything with just a set of usernames -- the private keys
are kept individually on the individuals phones.
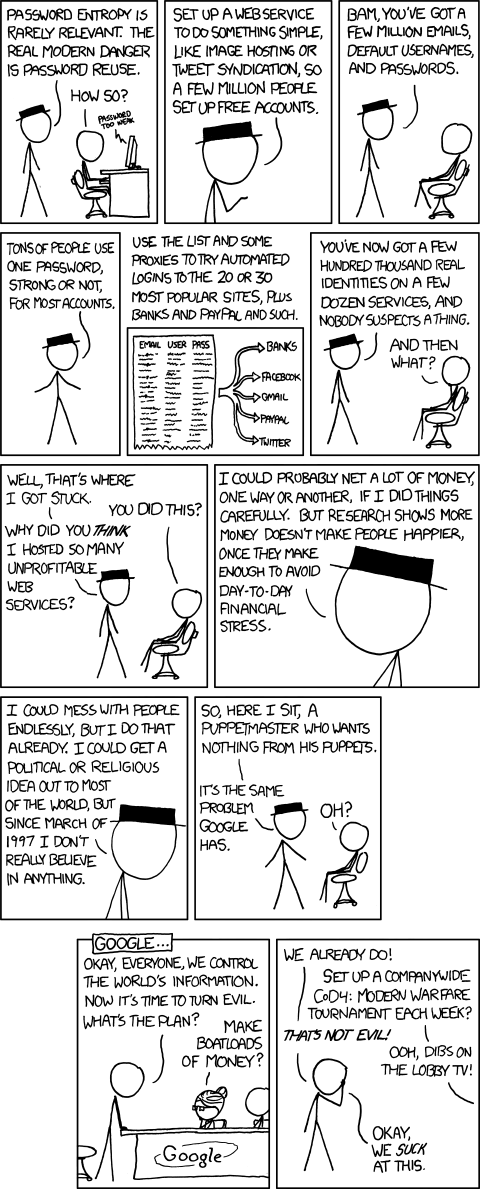
(BTW, selling of credentials by corrupt officials of a software company is quite common -- Internet is seriously leaking out usernames and passwords! It is foolish to think that people who harvest this cannot find purchasers or find no use for such lists -- as hinted in the above comic)
Another
big advantage of Homing Space is that lot of coding gets reduced. There is NO need to implement an "email check" during registration. NO "forgot password" loop, and so on. A potential user can enter
a site -- there is no separate registration and login process.
A big third advantage is that even new sites can potentially get a lot of users fast -- because the websites implementing Homing Space based accounts are getting from the same large pool of users with Homing Space personas. So when one merchant starts using Homing Space, everyone else benefits too! Network effects multiplied!
Lastly
(but not least!) Homing Space actually should open up many applications such as realistic P2P applications, blockchain applications and so on
As a merchant I am excited. How do I start? Where are the technical docs for Homing Space?
To implement Homing Space you (or someone responsible at your organization) need to first need to fill out a form at our website. The technical documentation here has the rest of the steps!
So what is the mission statement for Homing Space?
We want to totally get rid of the need of all passwords for now and forever-- except for the ONE password that you need to remember.
I invented Homing Space because I was afraid that when it is finally
my turn to go from this world, my head may turn on the side and hundreds of usernames and passwords may pop out of my ear on the pillow; and dirty the pillow :-) My children would be totally locked out of all the
data I have left behind in various locations. It was a horrid nightmare that I dread. Hence, Homing Space!
*What is ATM?
*ATM = Automatic Teller Machine. That box where you insert a debit card of your bank and get money from your bank balance. Also known as "Cash Machine" or "Cash Point" or "DABs or distributeur automatique de billet" or "Cajero automático"
Acknowledgements
The images for explaining asymmetric encryption and signing is from https://dzone.com/articles/a-gentle-introduction-to-asymmetric-encryption-and The comic strips are from https://xkcd.com